It has recently been announced that a new semi-annual channel release for System Center is available. As you can see in the following picture, the new System Center 1807 is the last release before GA of SC 2019. So, my recommendation is to implement this release and test it before going further . In short, you have a plenty of time to evaluate the newest SC and prepare your staff for SC 2019 deployment in production.

TIP: SC 1807 is an update release for SC 1801. To apply System Center, version 1807 you will first need to download SC 1801
System Center 1807 provides updates to the following products:
:: Virtual Machine Manager
In this post, we will cover the major changes for VMM.
Storage Space Direct Management
With Virtual Machine Manager 1807, you will now be able to patch and update the nodes of a Storage Spaces Direct cluster with the orchestration of the update process performed by VMM. You can update individual S2D hosts or clusters against the baselines configured in windows server update services (WSUS)
VHD Placement
When you add a new VHD to the existing VM, you can now define CSV path (a new volume) for that disk to eliminate problems with storage space. Prior to VMM 1807, a new VHD of an existing virtual machine would be placed in the same CSV as the other VHDs, aggravating the problem if the CSV was already running high on utilized storage.

Convert SET switch to logical switch
VMM 1807 allows you to convert a switch embedded teaming (SET) switch to logical switch by using the VMM console. In earlier versions, this feature was supported only through PowerShell script.
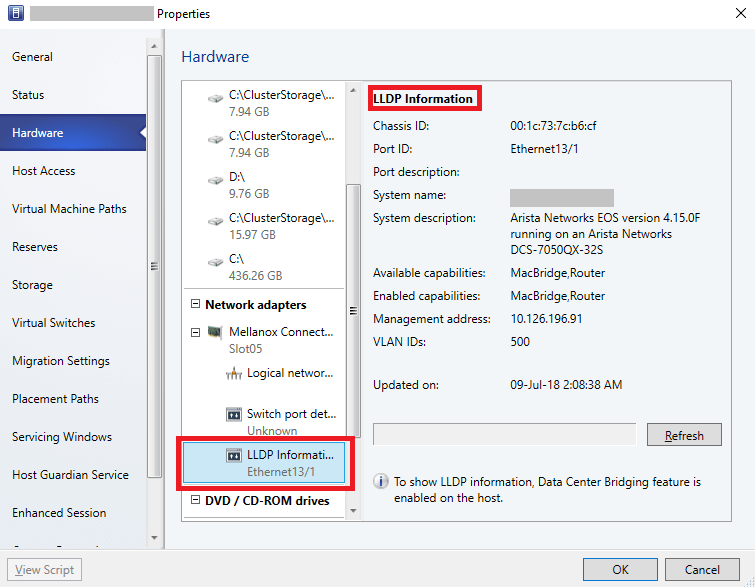
Display of LLDP information for networking devices
VMM 1807 supports Link Layer Discovery Protocol (LLDP). You can now view network device properties and capabilities information of the hosts from VMM. Host operating system must be Windows 2016 or higher. DataCenterBridging and DataCenterBridging-LLDP-Tools features have been enabled on hosts to fetch LLDP properties
VMware host management
VMM 1807 supports VMware ESXi v6.5 servers in VMM fabric. This support facilitates the administrators with additional flexibility in managing multiple hypervisors in use.
To evaluate SC 1807, you can download SC 1801 from here , and then update to 1807 (SAC) + it also will be available @MSDN.
In addition, VMM 1807 has received SQL Server 2017 support.
TIP: VMM 1807 update package for VMM 1801 can be obtained here

